Last Updated on 25/02/2026 by Alex
Welcome! Last month, I demonstrated how to deploy the FortiClient VPN and Profiles via Microsoft Intune, this week I’ll show you how to deploy Barracuda VPN and Profiles instead, I hope you find this guide useful, let’s get into it!
Prerequisites
- Basic understanding of Win32 application packaging
- Microsoft Intune licence
- Permissions to create applications within Microsoft Intune.
- Test device and user.
- Download of the Network Access Client installation files (Barracuda login required)
Extracting the MSI file from the Barracuda VPN installer
The first step to deploying the Barracuda VPN is to extract the MSI from the Network Access Client .exe setup file, the version that I have is NetworkAccessClient_5.1.2-18_x64.exe, to extract MSI from this setup file, run the following command: [BarracudaNACInstaller].exe /s /x /b”C:[foldertoextract]” , a window will appear asking if you’d like to uninstall the product, select no, you’ll then have the BarracudaNAC.msi in the directory that you selected:

Creating the Barracuda VPN Profile on a test device
Install Barracuda NAC Client
We need to capture the required registry keys to apply to our deployment package to be able to mass deploy the VPN profile settings alongside the client, to do this, install the BarracudaNAC.msi as you normally would, choose the setup type and master password (if required by the network team), for me, I have selected VPN Client for setup type and no master password, so essentially, next, next, finish.
Create \ Import the VPN Profile
Next step is to create or import an existing VPN profile, this will allow us to export the registry keys required for mass deployment.
Create a VPN Profile
If this is your first client configuration, load up the Barracuda Network Access Client with elevated privileges and select New Profile, select Machine:

A new window will appear, enter in the VPN settings as instructed by your network team, once done, click save.

At this stage, I will assume that the VPN settings are correct and working. For me, I already have a VPN Profile exported, ready to be imported.
Importing an existing VPN Profile
My network team very kindly gave me a VPN profile that I could use to import, to import, open the Barracuda Network Access Client using elevated privileges, right-click the white space, select Import and then Machine.

Confirm that the VPN settings are correct and successfully imported:

Again, I am assuming at this stage that the VPN is functional.
Creating the VPN Profile Configurations for deployment
Now that we have our VPN profile present within the Barracuda NAC, we need to create an .MST file to apply these customisations for mass deployment. I will use my favourite MSI editor tool to add the configurations to deploy the Barracuda VPN profile along with the client, I use Master Packager to do this but beware that there are other tools out there.
Extracting the registry entries
After creating / importing the VPN profile into the Barracuda Network Access Client tool, registry keys and values have been created by the client that contain the settings that we need to deploy on mass, we need to extract these settings, to do this, open regedit, navigate to HKEY_USERS.DEFAULT\Software\Phion and extract the contents to a .reg file

Save the .reg file, we’ll need this later.

Create the transform file
Open the BarracudaNAC.msi within Master Packager application, go to Transform, New Transform and save to a safe location using an .MST format, I’ve used BarracudaVPNSettings.mst for my lab.
Importing the VPN Profile registry keys into the MST File
Within Master Packager, after creating your MST file and with your .reg key that you exported earlier from the test device, go to Registries on the left hand side:

Right-click the white space within the registries box and select Import Registry:

Select the .reg key that you exported earlier:

Verify that your registry keys are present within Master Packager:

Now that your registry keys have been imported, we need to change a couple of bits so they work correctly, still within Master Packager, right-click one of the registry keys that you imported (tip: anything with a component of HKU_C assigned) and select Open in Table Editor:

This will take you to registry table view, all of the entries in green are entries that we have created in our MST, on that page, go to the component view and find the HKU_C line:

On the HKU_C component entry and double-click on the Attributes value, an editor will appear, select the following and ensure that the entry is 256:

Double-click on the HKU_C component again, but this time in the KeyPath section, ensure that the entry is blank (do not type anything in and select enter to overwrite the cell), this will change the entry to <null>:

Confirm that the HKU_C component looks like the following before proceeding:

Save your .MST file and have it ready for Win32 app packaging:

Creating the Win32 App Package within Intune
This section is how to wrap the installation files into a Intune format and then creating the Win32 app within Intune.
Creating the .Intunewim file
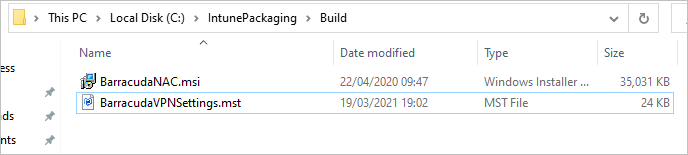
Now that we have our .MSI and our custom .MST file, we need to wrap these files into an format that Intune can use to deploy to clients, I won’t go into the win32 app wrapping process here, but create a directory with the two files present (the .msi and .mst, do not include any other files in the directory), like so:
Using the Win32 Content Prep Tool, run the following commands:

Within your directory, this should now include the .intunewim file, this will be used to upload the installation files to Intune:

Creating the Win32 Application
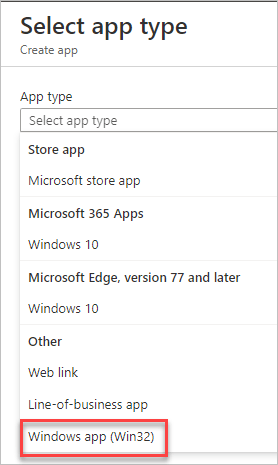
Within the MEMAC portal, go to Apps, Windows, select Add:

Select Windows App (Win32):
Select the .Intunewim file created previously:

File in some metadata on the application:

On the Program page, add in the following entry to your installation command: msiexec /i “MSIFileName.msi” TRANSFORMS=”MSTFileNameCreatedInMasterPackager.mst” /qn, here’s mine as an example:

On the requirements page, select 64-bit only and your desired minimum supported OS:

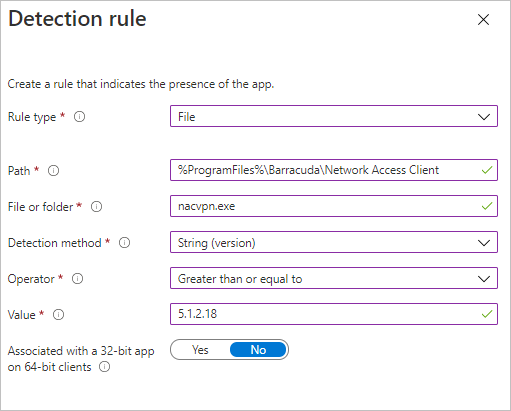
For Detection Rules, enter in the following:
| Setting Name | Value |
|---|---|
| Rule Type | File |
| Path | %ProgramFiles%\Barracuda\Network Access Client |
| File or folder | nacvpn.exe |
| Detection method | String (version) |
| Operator | Greater than or equal to |
| Value | 5.1.2.18 (Update this for the version that you are deploying) |
| Associated with a 32-bit app on 64-bit clients | No |
My config:
No requirements for Dependencies or Supersedence. On the assignments page, assign the application to your test pool of devices that are enrolled into Intune or will be via Autopilot, then verify that all is well on the review section and select Create.

The Results
Once the Barracuda VPN has been deployed to the test device, the following should be in place.
Barracuda Network Access Client Installed and present in the system tray and add \ remove programs:

Barracuda VPN profile preconfigured:

Successfully reporting as installed within MSIntune:

That’s how you can deploy Barracuda VPN with predefined VPN profiles via Microsoft Intune! Thanks for reading, until next time.




i get an error of failed when installing, but i can run the command locally and it works…i also need to install the windows login software afterwards to be able to choose single sign on…I got a bit lost on the changing the: On the HKU_C component entry and double-click on the Attributes value, an editor will appear, select the following and ensure that the entry is 256…if i just click 256 it changes it to 260…not sure what is going wrong…i followed your directions to a T
Hi Joel,
Does your MSI and MST package work fine outside of Intune? If so, I would recommend you look at the detection method within the Intune app, if you check the path and version manually does it match? If not, the version and \ or the path may need updating in the query to reflect the application that you have, I know Barracuda do tend to update their Program Files directory structure quite often so this is most likely the cause, you can also use a registry key too, if desired. The detection method needs to tell Intune that “yes, I am here” to be considered a successful install.
Thanks,
Alex.
Hi Alex,
Thank you for this post. Very helpful.
Just a quick note:
To extract the MSI from the .exe file I needed to add .\ before the NetworkAccessClient_5.2.2-17_x64.exe
So the full command looked like this:
.\NetworkAccessClient_5.2.2-17_x64.exe /s /x /b”c:\Latest”
Without the .\ I always got an error……
Many thanks
Attila
Couldn’t reply Sorry…i had to use edge and then luckily the leave a reply showed up. I got it to install and the registry settings were there, but if i try to install the windows client sign on (where you can set up the connect to the vpn before login) i get the feature you are tyring to install is on a network resource that is unavailable. enter an alternate path to folder containing install package Barracudanac.msi…so barracuda has the directions for installing with a silent.cmd option with the exe install…is there i reason i want to install this through the msi? I’m not sure what is happening with my install that it no longer has the barracudanac.msi file in the c:\windows\imecache\33b49d17…. I am going to try to install it through intune via exe file and not extract the msi from the exe…not sure if all copies over like a full bulk install…
Step 1. Prepare the silent.cmd File:
Save the following to silent.cmd file:
@echo off
REM installs VPN-only version of NAC (VPN components + Virtual Adapter)
REM use “PROGTYPE=ENTEGRA” instead to also install NAC/Firewall components
start /wait BarracudaNAC.exe /clone_wait /s /v”/qr PROGTYPE=VPN REBOOT=Suppress”
REM uncomment to import custom application settings (e.g. VPN profiles)
REM reg import mysettings.reg
REM uncomment to add Credential Provider
REM start /wait BarracudaNAC.exe /clone_wait /s /v”/qr PROGTYPE=VPN ADDLOCAL=CommonCore,DrvCudaVPN,x64VPN,x64CredProv REBOOT=Suppress”
COPY
The registry file (mysettings.reg) is used for optional import of custom application settings (e.g. VPN profiles) as they can be found in HKEY_USERS\.DEFAULT\Software\Phion\.